DeFi's security crisis: Lessons from April's $630M meltdown

Crypto hacks are becoming larger, slower, and far more sophisticated. In 2026, attackers are no longer relying solely on smart contract bugs or leaked private keys — some operations now involve months of social engineering, infrastructure manipulation, and coordinated laundering strategies across multiple chains.
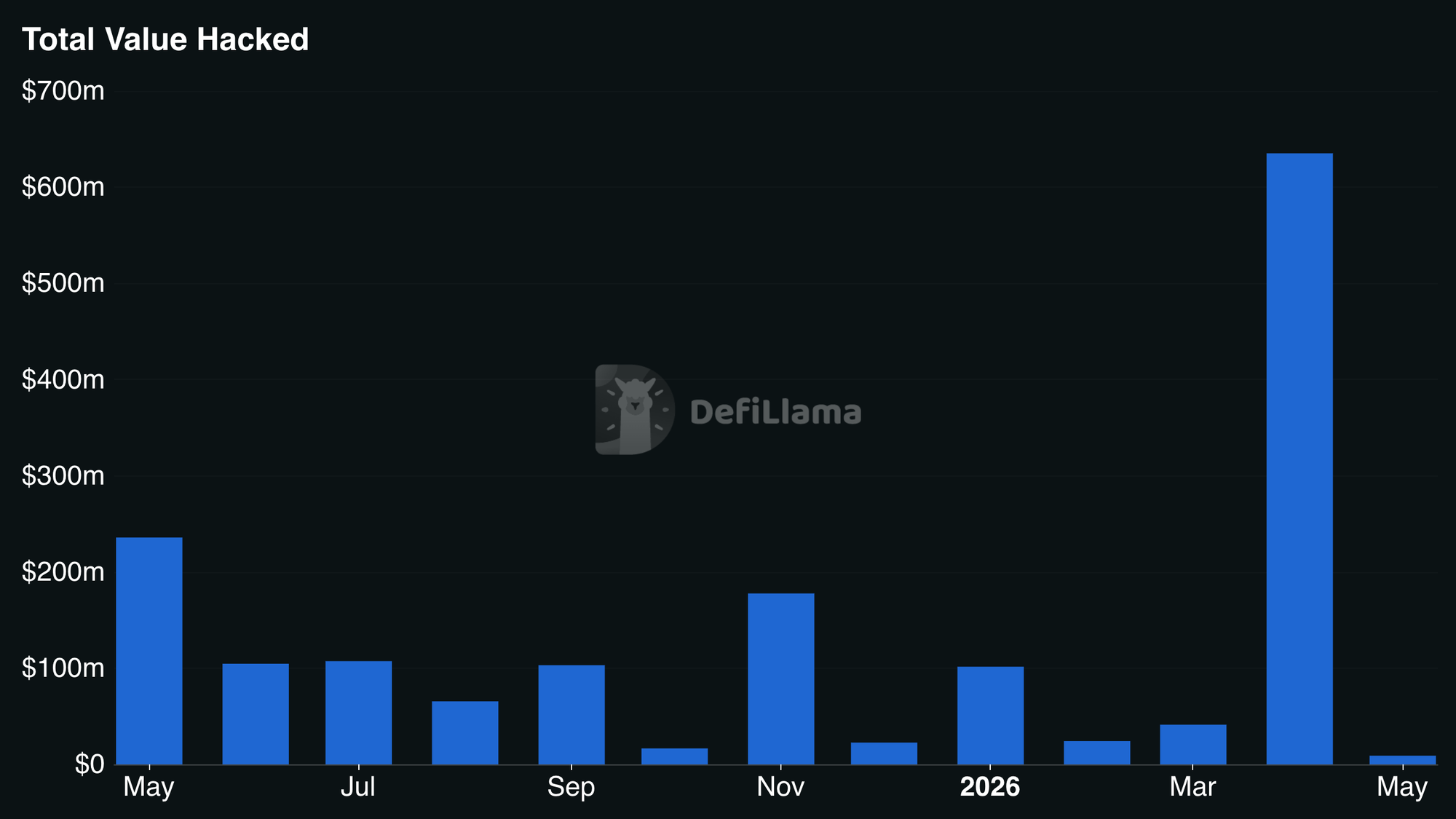
April marked a turning point. Over $600 million evaporated in just 18 days, making it the worst month for crypto hacks since February 2025. Two massive exploits accounted for the majority of those losses, exposing how vulnerable even established DeFi protocols remain.
North Korean hackers prevail
According to TRM Labs research, hackers linked to North Korea (DPRK) are responsible for approximately 76% of all 2026 hack losses so far. Two distinct groups are believed to have walked away with $577 million in two attacks — the Drift Protocol breach on April 1 ($285 million) and the KelpDAO bridge exploit on April 18 ($292 million).
Those two massive breaches make up just 3% of the total incident count as of April 30, but 76% of stolen value. In five years, DPRK's share of total crypto losses (under 10% in 2020) has shot up dramatically.
Its dominance comes down to scale rather than frequency. The hackers' operational tempo hasn't changed much. Each year, they carry out a relatively small number of highly coordinated attacks on high-value targets.
In 2025, North Korea's share jumped from 39% to 64% largely due to the record-breaking Bybit breach — the largest single crypto hack ever. A compromised signing interface allowed the hackers to siphon $1.46 billion from the exchange's cold wallet.
The attacks have evolved far beyond private key compromises. Their growing sophistication has led blockchain analysts to question whether they might now weaponize AI tools for reconnaissance and social engineering.
Drift Protocol hack (total loss: $285 million)
Beyond the sheer amount of stolen funds (over 50% of Drift's TVL), this attack was unusual because it involved months of social engineering. As early as fall 2025 — half a year before the theft — North Korean proxies began meeting with Drift Protocol staff, leading to compromised admin keys.
The social engineering play: Months of communication
According to Drift's own investigation, those individuals posed as a quant trading firm. Approaching employees at crypto events, they seemed to initiate legitimate integration talks. This cover allowed them to keep up ongoing contact, both online and offline.
On-chain preparation began on March 11, when attackers pulled funds from Tornado Cash to bankroll part of their infrastructure.
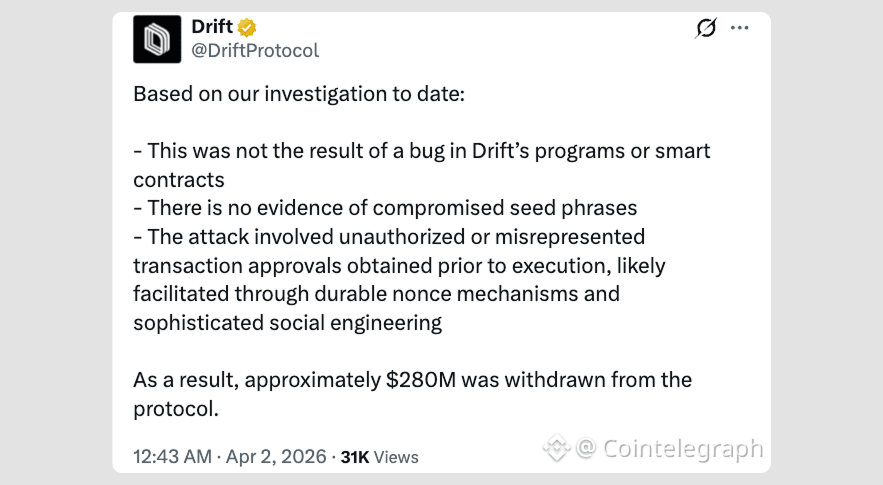
The technical bit: Manipulating durable nonces
The breach exploited durable nonces, a Solana-native feature that lets transactions stay alive indefinitely instead of expiring. The standard expiry kicks in within roughly 90 seconds if the transaction isn't confirmed on-chain.
Durable nonces are meant for offline hardware signing — the extended window allows a transaction to be pre-signed and held before broadcast. The attackers tricked Drift's Security Council multisig signers into pre-authorizing transactions between March 23 and 30.
Council members — a small group of trusted individuals — unknowingly pre-signed transactions that gave up admin control. During that period, the Security Council switched to a 2/5 threshold configuration with no time lock, which the hacker also exploited.
Meanwhile, the group launched a fake token and whitelisted it so the protocol's oracles would treat it as collateral. The price of this low-liquidity asset (CVT) was pumped through wash trading. The attackers deposited 500 million CVT to pull out real assets.
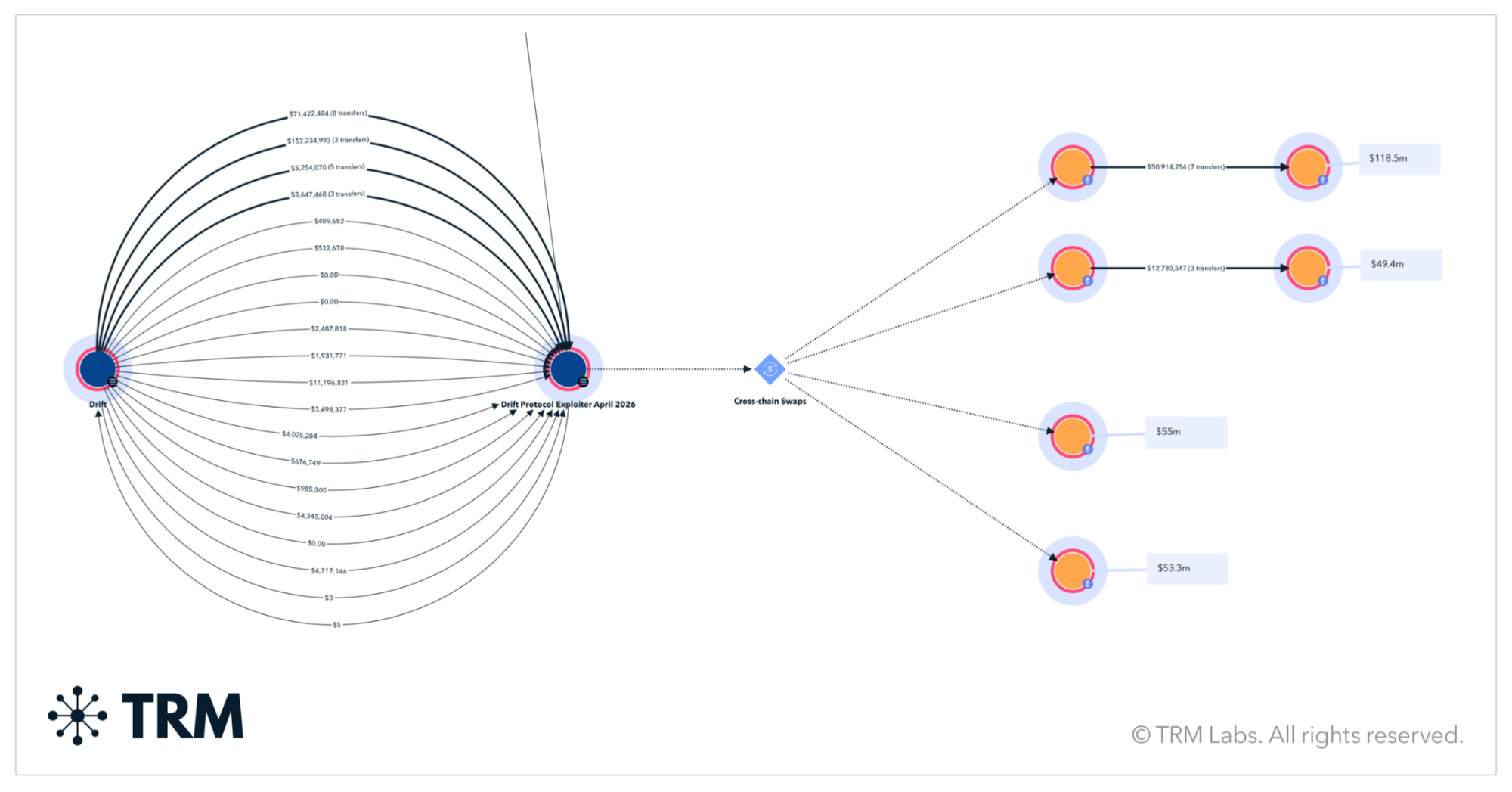
On April 1, the attackers executed the pre-signed transactions. In roughly 12 minutes, 31 withdrawals pulled out Drift's assets, including USDC, SOL, and JLP. Within hours, most of them were bridged to Ethereum.
Latest on Drift Protocol breach response
Immediately after detecting the attack, Drift suspended all deposits and withdrawals. The team is focused on restoring platform stability and developing a recovery plan for affected users, working with Solana's STRIDE security mechanism.
As of early May 2026, the protocol has teamed up with security firms Asymmetric Research and OtterSec to put together a coordinated recovery plan. Each affected user will receive "recovery tokens," which act as a pro-rata claim on the recovery pool.
This pool will be funded with remaining protocol assets, future platform net revenues, contributions from partners, and up to $127.5 million in matching deployment from Tether. Once the total surpasses $5 million, redemption will become available.
Key takeaways from the incident
Risks in DeFi aren't limited to smart contracts. The systems and people around them can also be manipulated.
Drift's security safeguards did not red-flag the transactions because they carried valid admin signatures. As noted by Chainalysis, this underscores the need for "pre-execution evaluation tools, like Hexagate's GateSigner, which assess the intent of transactions to block abnormal activity in real-time."
This attack shows a shift to a more cautious and measured approach to money laundering. The stolen funds haven't moved yet — and TRM analysts suggest cashing out could take months or even years.
The exact DPRK subgroup responsible remains unknown. Their behavior differs from the prolific TraderTraitor — an alleged subgroup of the Lazarus Group that orchestrated the Bybit hack of 2025, according to the FBI.
KelpDAO breach (total loss: $292 million)
This breach didn't involve in-person social engineering — instead, it was purely technical, going after the protocol's rsETH LayerZero bridge on Ethereum.
Here's how it unfolded:
- Poisoning specific nodes: The attackers swapped out software used by two internal RPC nodes so they would feed back false blockchain data.
- Attacking external nodes: Uncompromised RPC nodes were hit with a distributed denial-of-service attack, which forced the bridge verifier to lean on the two poisoned nodes.
- Feeding false data: The compromised nodes reported a completed rsETH burn that never happened. Reading from this corrupt source, the verifier signed off on the fraudulent cross-chain message.
The hackers drained roughly 116,500 rsETH from the bridge contract.
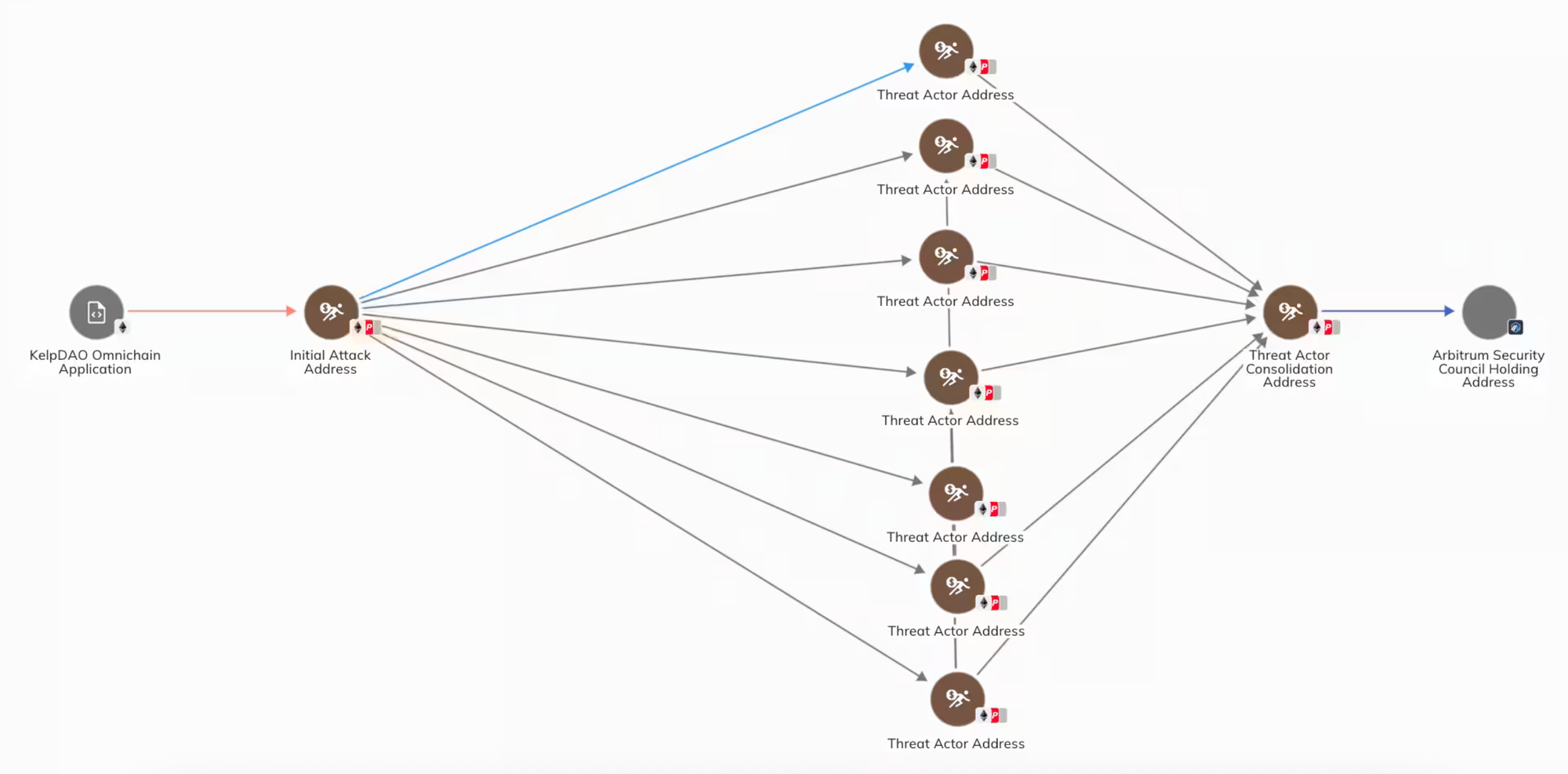
What made this attack possible was the use of a single DVN (decentralized verifier network). KelpDAO used only the LayerZero Labs DVN for message validation. Without a second verifier, the attackers only needed to poison one data source to pull off the fraudulent transaction.
The laundering strategy was also different. The hackers left roughly 30,766 ETH (about $75 million) on Arbitrum, an Ethereum Layer-2 chain that's significantly more centralized compared to the mainnet. Arbitrum's Security Council froze those stolen funds, triggering what TRM Labs called a "mad laundering scramble."
The hackers rushed to convert their remaining loot to Bitcoin, managing to swap around $175 million worth of ETH. Those transactions were mainly routed through THORChain, since the liquidity protocol has no KYC requirements. The attackers also managed to obscure some wallet linkages pre-conversion using the Umbra privacy tool.
Latest on KelpDAO breach response
As of May 11, 2026, the Arbitrum DAO has passed a vote to release roughly 30,765 ETH ($70+ million) frozen by their Security Council. Those coins are being moved to a "DeFi United" recovery initiative to help repay victims, as the stolen rsETH was used as collateral to drain funds from Aave.
However, the funds are also subject to an active US federal court order, and Aave has yet to prove the funds belong to harmed users.
DeFi contagion spreads
Major hacks like KelpDAO are increasingly causing systemic liquidity issues across other DeFi platforms — similar to a bank run.
Earlier incidents of 2026 looked minor in comparison:
- In January, compromised treasury access at Step Finance cost roughly $27 million.
- That same month, a contract vulnerability siphoned $26 million out of Truebit, an Ethereum-based verification protocol.
- In March, Resolv Labs' minting contract flaw allowed hackers to steal over $25 million, causing its USR stablecoin to crash 70%.
The whole ethos of DeFi has been built around trust-minimized systems — yet even established projects remain exposed to smart contract bugs, cross-chain infrastructure glitches, and operational blow-ups.
Following the Drift Protocol and KelpDAO meltdowns, the ripple effects spread quickly across the decentralized economy. Platforms felt the pain of user exodus — shedding billions in total value locked (TVL). As the KelpDAO news broke, lenders like Aave paused rsETH markets.
New attacks followed. In late April, Wasabi Protocol pools on Ethereum and Base were drained in a heist that followed the Drift playbook closely. The attackers compromised a deployer key with no timelock or multisig, granted themselves admin privileges, and walked away with $4.5 million.
Cross-chain bridges: A recurring point of failure
Secure transfer of assets across chains remains a headache. Bridges have been DeFi's Achilles' heel for years, with over $2.8 billion lost collectively through incidents like Ronin, Wormhole, and Nomad. Despite using different mechanisms, these incidents produced the same fundamental failure: unauthorized supply entering circulation.
As Chainalysis explains:
"Once that invariant breaks, downstream effects are mechanical. rsETH holders on Layer 2s are suddenly claiming against collateral that doesn't exist. Peg deviation follows. Liquidity fragments. Contagion risk spreads to any protocol that accepts the token as collateral."
DeFi bridges are prime targets because they lock up high-value assets across blockchains and run on a seemingly simple rule: "Assets released on the destination chain must equal assets burned or locked on the source chain."
Bridges are multi-layered when it comes to verification, and each layer — validators, oracles, or message-passing systems — has its own trade-offs. This creates a large, complex attack surface where design flaws, signature forgery, and validation errors allow fund draining.
Due to liquidity concentration, a single bridge failure can take down multiple downstream protocols. The trilemma of security, speed, and decentralization keeps plaguing the industry — especially as protocols get more interconnected.
Beyond bridges: The many faces of DeFi risk
Bridges aren't the only weak spot. Private key compromises, oracle manipulation, flash loan attacks, and governance takeovers have all wreaked havoc on DeFi.
- Private key leaks remain disturbingly common. When a project stores admin keys on a compromised server — or worse, in a GitHub repo — attackers walk right in.
- Oracle manipulation exploits price feeds that rely on thin liquidity pools, allowing attackers to borrow against artificially inflated collateral.
- Flash loan attacks use borrowed capital to manipulate markets, extract value, and repay the loan — all in one transaction.
Most attacks don't require breaking cryptography as they exploit human error, rushed code, misconfigurations, or over-reliance on single points of failure. DeFi's promise of "trustless" systems has only shifted risk from counterparties to code and its operators.
Wrapping up: DeFi's security wake-up call
DeFi's edge has always been its openness, composability, and speed. But those same features become liabilities when security lags behind growth. April 2026 was a brutal month for DeFi. Over $630 million in losses, two record-breaking hacks, and a clear message: the industry has a security problem.
North Korean hackers aren't going away. Their playbook — combining social engineering, technical exploits, and patient laundering — worked at Drift. It worked at KelpDAO. It will work again unless protocols harden their defenses.
That said, the numbers aren't all doom and gloom. April's hack volume, annualized, points to roughly $750 million. With DeFi TVL forecasted to grow 31% this year — in line with average growth since 2021 — the ratio of hack volume to TVL is on a steady decline: from 7.24% in 2022 to a projected 1.49% in 2026. The trajectory appears to be improving — but risks remain.
What needs to change?
First, multi-layered verification for bridges — one DVN is a single point of failure. Second, real-time intent evaluation tools that flag suspicious admin transactions before they execute. Third, harder targets — making social engineering campaigns costly and unrewarding.
The attacks are unlikely to stop anytime soon. But better safeguards could limit the damage.